Immunity for the AI era
An AI-powered security layer trained on real adversaries, designed to detect and adapt to evolving threats.

FEATURES
Threat intelligence
USE CASES
One product, every attack surface
Account security

Payment fraud
Stop chargebacks and card cracking without blocking real customers. Device fingerprinting and true location catch bad actors at checkout - not after.
SMS fraud
Bots trigger OTP at scale, racking up costs per message. Device intelligence flags them before the text sends - fewer messages, better security
Geo compliance
See where users actually are - even behind VPNs. Automatically enforce jurisdiction rules and block access from sanctioned regions in real time.
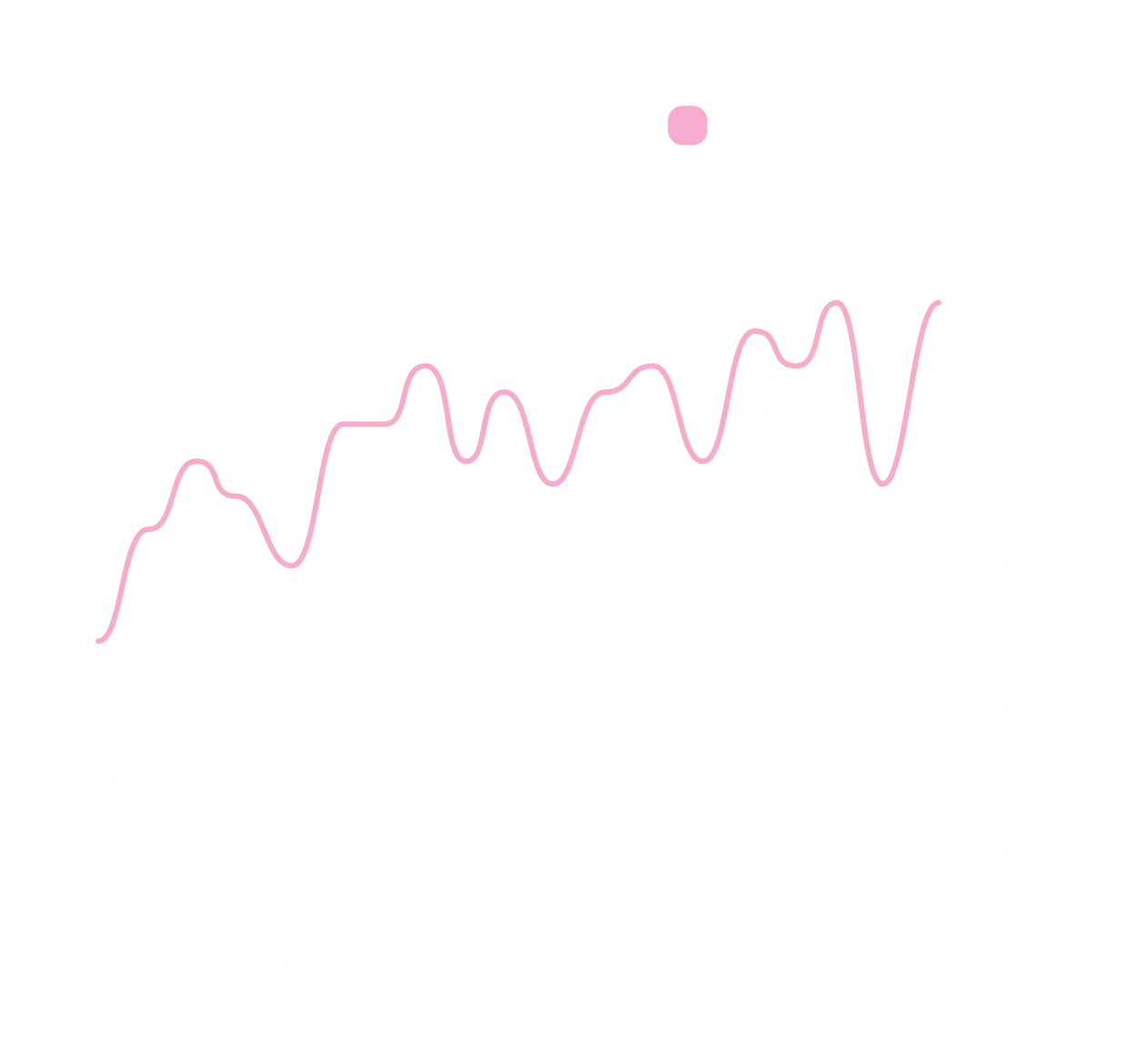
REDTEAM
A self-healing system
RedTeam operates as an adversarial R&D system, continuously simulating real-world attack techniques — from VPN evasion to synthetic identities and coordinated device networks.
TEAM
Who we are

Oliver Quie
CEO
10 years in Identity & Behavioural Analytics

Oscar Hayek
CTO
AI engineering, Fmr-Aus Government

Tom Ryan
CPO
Fmr-Cambridge ML Researcher

Tony Pepper
Board Member
Co-founder Egress